☑ That's Good Enough
- What’s New in Python 3.13 - Library Changes Part 2 Wed Mar 12 2025
- What’s New in Python 3.13 - Library Changes Part 1 Sun Feb 23 2025
- What’s New in Python 3.13 - Performance Improvements Sat Nov 16 2024
- What’s New in Python 3.13 - Intepreter Updates Tue Oct 29 2024
- BlazingMQ: Client/Broker Protocol Sun Oct 20 2024
- BlazingMQ: Hands On Thu Oct 10 2024
- BlazingMQ: Clustering and Message Flow Wed Jul 03 2024
- BlazingMQ: Introduction Thu Jun 27 2024
- What’s New in Python 3.12 - Library Changes Sun Mar 17 2024
- What’s New in Python 3.12 - F-Strings and Interpreter Changes Tue Feb 06 2024
March 2025

☑ What’s New in Python 3.13 - Library Changes Part 2
In this series looking at features introduced by every version of Python 3, we take a look at some of the new features added in Python 3.13. In this article we look at the remaining changes to the standard library, comprising changes in CLI tools, concurrency, networking & IPC, Internet data handling, XML processing, IP address handling, development & debugging tools, and runtime and language tools.
This is the 36th of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 44 minutes )
February 2025

☑ What’s New in Python 3.13 - Library Changes Part 1
In this series looking at features introduced by every version of Python 3, we take a look at some of the new features added in Python 3.13. In this article we look at the first half of the changes in the standard library, comprising a new exception, as well as changes to regular expression support, data types, mathematical modules, data persistence, the configparser module, file & directory access, and operating system services.
This is the 35th of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 42 minutes )
November 2024

☑ What’s New in Python 3.13 - Performance Improvements
In this series looking at features introduced by every version of Python 3, we take a look at some of the new features added in Python 3.13. In this article we look at the improvements to the intereter itself. We’ll look at the new option to disable the GIL, and the addition of a JIT compiler.
This is the 34th of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 32 minutes )
October 2024

☑ What’s New in Python 3.13 - Intepreter Updates
In this series looking at features introduced by every version of Python 3, we take a look at some of the new features added in Python 3.13. In this article we look at the improvements to the interactive interpreter and improved error reporting.
This is the 33rd of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 8 minutes )

☑ BlazingMQ: Client/Broker Protocol
BlazingMQ is a message queue middleware system developed at Bloomberg which was opened sourced around a year ago. I think it has a lot of very useful features for some use-cases, so this series of articles looks at it in a bit more detail. In this fourth article I’m going to discuss the low-level details of the network protocol between clients and brokers.
This is the 4th of the 4 articles that currently make up the “BlazingMQ” series, the first of which was BlazingMQ: Introduction.
Read article ( 37 minutes )

☑ BlazingMQ: Hands On
BlazingMQ is a message queue middleware system developed at Bloomberg which was opened sourced around a year ago. I think it has a lot of very useful features for some use-cases, so this series of articles looks at it in a bit more detail. In this third article I’m going to try to get a basic producer and consumer working with the broker to get some basic exposure to the APIs in C++ and Python.
This is the 3rd of the 4 articles that currently make up the “BlazingMQ” series, the first of which was BlazingMQ: Introduction.
Read article ( 25 minutes )
July 2024
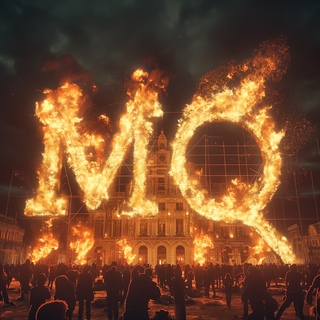
☑ BlazingMQ: Clustering and Message Flow
BlazingMQ is a message queue middleware system developed at Bloomberg which was opened sourced around a year ago. I think it has a lot of very useful features for some use-cases, so this series of articles looks at it in a bit more detail. Having looked at an overview of the features in the previous article, I’m going to drill into clustering and a high-level look at the way messages flow through the system.
This is the 2nd of the 4 articles that currently make up the “BlazingMQ” series, the first of which was BlazingMQ: Introduction.
Read article ( 21 minutes )
June 2024

☑ BlazingMQ: Introduction
BlazingMQ is a message queue middleware system developed at Bloomberg which was opened sourced around a year ago. I think it has a lot of very useful features for some use-cases, so this series of articles looks at it in a bit more detail.
This is the 1st of the 4 articles that currently make up the “BlazingMQ” series.
Read article ( 31 minutes )
March 2024

☑ What’s New in Python 3.12 - Library Changes
In this series looking at features introduced by every version of Python 3, we take a look at the new features added in Python 3.12 in the standard library, as well as a few other minor language improvements I missed in previous articles.
This is the 32nd of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 49 minutes )
February 2024

☑ What’s New in Python 3.12 - F-Strings and Interpreter Changes
In this series looking at features introduced by every version of Python 3, we take a look at the new features added in Python 3.12 related to f-strings, inlining of comprehensions, improved error reporting, the new monitoring API for debuggers, and better isolation for sub-interpreters.
This is the 31st of the 36 articles that currently make up the “Python 3 Releases” series, the first of which was What’s New in Python 3.0.
Read article ( 38 minutes )
